Lifetime Reading Certificate 1-8 Reading Self Contained

The Java Developer's Guide to SSL Certificates
Overview
When developing spider web applications, we often need to integrate with other applications using SSL. This could be over different protocols such every bit HTTPS, IMAPS, or LDAPS.
In this article, nosotros'll comprehend what Java developers demand to know most SSL certificates.
Certificate Chain
An SSL connexion succeeds only if the client can trust the server. Let'south take a look at how this trust model works.
In Chrome, go to google.com and bring up the Programmer Tools (F12 on Windows, Cmd+Option+i on Mac).
Under the Security tab, click the View Certificate button to testify details virtually the certificate.
We can see that the site certificate is function of a concatenation. This particular concatenation consists of 3 certificates.
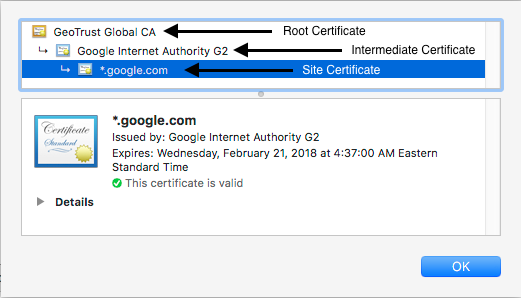
The site certificate has been issued by a certificate named Google Net Dominance G2. This is the intermediate certificate. In plough, the intermediate certificate is issued by the root certificate GeoTrust Global CA.
When we establish a connectedness over HTTPS, the web server volition respond by providing its site and intermediate certificates. Information technology is and then upwardly to the client to complete the chain by having the root certificate. This concatenation validation is necessary for the customer to trust the site.
Since Chrome has the root certificate GeoTrust Global CA in its certificate store, our connection succeeds and we are not presented with any errors or warnings.
Notation: There may be more than i intermediate certificate in the chain depending on the site.
Cocky-signed Certificates
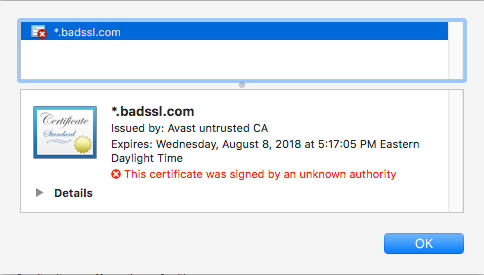
Certificates not issued by known CA merely rather past the server hosting the certificate are called self-signed.
These are oftentimes used in internal development environments that are non customer facing.
The root certificates for these will be absent in the browser's certificate store.
An example of cocky-signed document is at https://self-signed.badssl.com. We can see that this was issued by Avast Untrusted CA which the browser does non recognize and so information technology displays a warning.
Coffee Truststore & KeyStore
In this section, we'll discuss where certificates alive on a organization where the JDK/JRE is installed.
Truststore
The truststore is a file that contains the root certificates for Certificate Authorities (CA) that issue certificates such equally GoDaddy, Verisign, Network Solutions, and others.
The truststore comes arranged with the JDK/JRE and is located in $JAVA_HOME/lib/security/cacerts.
The truststore is used whenever our Coffee code establishes a connexion over SSL.
Keystore
The keystore is a file used by an application server to store its private fundamental and site certificate.
And then if we were running a spider web awarding over SSL at tomcat.codebyamir.com, the keystore file named keystore.jks would comprise two entries — i for the private key and one for the certificate.
The keystore is used by Java application servers such as Tomcat to serve the certificates.
Note: Most Java awarding servers simply read the contents of these files during startup. This means that whatsoever updates to the file crave a restart to take outcome.
Keytool
Keytool is a utility arranged with the JRE for managing central pairs and certificates. This allows us to view/modify/create certificate stores in the Coffee world.
List the certificates in the truststore
keytool -list -keystore $JAVA_HOME/lib/security/cacerts We'll be prompted for a password for the truststore. The default password is "changeit".
This truststore contains 104 entries and each entry has a unique alias and fingerprint. Nosotros've truncated the output beneath for brevity.
Keystore type: JKS
Keystore provider: SUN Your keystore contains 104 entries verisignclass2g2ca [jdk], Aug 25, 2016, trustedCertEntry,
Certificate fingerprint (SHA1): B3:EA:C4:47:76:C9:C8:1C:EA:F2:9D:95:B6:CC:A0:08:1B:67:EC:9D
digicertassuredidg3 [jdk], Aug 25, 2016, trustedCertEntry,
Certificate fingerprint (SHA1): F5:17:A2:4F:9A:48:C6:C9:F8:A2:00:26:9F:DC:0F:48:2C:AB:30:89
verisignuniversalrootca [jdk], Aug 25, 2016, trustedCertEntry,
Certificate fingerprint (SHA1): 36:79:CA:35:66:87:72:30:4D:thirty:A5:FB:87:3B:0F:A7:7B:B7:0D:54
digicerttrustedrootg4 [jdk], Aug 25, 2016, trustedCertEntry,
Certificate fingerprint (SHA1): DD:FB:16:CD:49:31:C9:73:A2:03:7D:3F:C8:3A:4D:7D:77:5D:05:E4
verisignclass1g3ca [jdk], Aug 25, 2016, trustedCertEntry,
Certificate fingerprint (SHA1): xx:42:85:DC:F7:EB:76:41:95:57:8E:13:6B:D4:B7:D1:E9:8E:46:A5
identrustpublicca [jdk], Aug 25, 2016, trustedCertEntry,
Certificate fingerprint (SHA1): BA:29:41:60:77:98:3F:F4:F3:EF:F2:31:05:3B:2E:EA:6D:4D:45:FD
utnuserfirstobjectca [jdk], Aug 25, 2016, trustedCertEntry,
Document fingerprint (SHA1): E1:2nd:FB:4B:41:D7:D9:C3:2B:30:51:4B:Ac:1D:81:D8:38:5E:2D:46
geotrustuniversalca [jdk], Aug 25, 2016, trustedCertEntry,
Certificate fingerprint (SHA1): E6:21:F3:35:43:79:05:9A:4B:68:30:9D:8A:2F:74:22:15:87:EC:79
digicertglobalrootg3 [jdk], Aug 25, 2016, trustedCertEntry,
Certificate fingerprint (SHA1): 7E:04:DE:89:6A:3E:66:6D:00:E6:87:D3:3F:FA:D9:3B:E8:3D:34:9E
deutschetelekomrootca2 [jdk], Aug 25, 2016, trustedCertEntry,
Certificate fingerprint (SHA1): 85:A4:08:C0:9C:19:3E:5D:51:58:7D:CD:D6:xiii:30:FD:8C:DE:37:BF
...
Using the google.com example from before, let's take a look at the fingerprint for the GeoTrust Global CA from our browser:
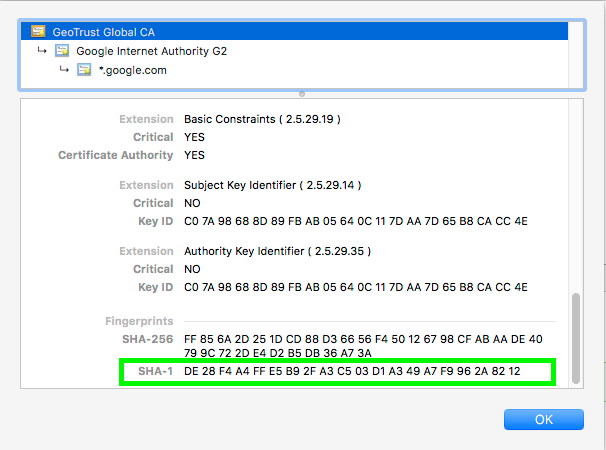
The SHA-1 fingerprint is DE:28:F4:A4:FF:E5:B9:2F:A3:C5:03:D1:A3:49:A7:F9:96:2A:82:12
Let's look for that in our truststore:
keytool -list -keystore $JAVA_HOME/lib/security/cacerts | grep -B1 -i DE:28
Enter keystore password: changeit
geotrustglobalca [jdk], Aug 25, 2016, trustedCertEntry,
Certificate fingerprint (SHA1): DE:28:F4:A4:FF:E5:B9:2F:A3:C5:03:D1:A3:49:A7:F9:96:2A:82:12 The output tells us that the certificate is in the truststore:
What does this mean to a Java developer?
Information technology means that lawmaking connecting to https://www.google.com won't throw an exception due to an SSL handshake mistake.
Add a document to the truststore
Adding a document to the truststore is necessary if we want to trust a certificate issued from a CA non present in the bundled truststore.
keytool -import -trustcacerts -file [certificate] -alias [alias] -keystore $JAVA_HOME/lib/security/cacerts Lawmaking Example
Below is some Java code that will connect to a URL and print the contents of the folio onto the screen.
Connecting to Site with a Trusted Certificate
Permit's try our code on another site with a valid SSL certificate.
Code
Replace line 12 from the code with this line:
private static final Cord URL = "https://httpbin.org/user-agent"; Output
We can see that the code output successfully shows that our user-agent cord is our Coffee version.
{
"user-agent": "Java/ane.8.0_131"
} Connecting to Site with an Untrusted Certificate
Let's try our lawmaking on a site with a cocky-signed certificate.
Lawmaking
Replace line 12 from the lawmaking with this line:
private static concluding Cord URL = "https://self-signed.badssl.com"; Output
The lawmaking throws an SSLHandshakeException because Java doesn't trust information technology.
Exception in thread "master" javax.net.ssl.SSLHandshakeException: sun.security.validator.ValidatorException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target
at sun.security.ssl.Alerts.getSSLException(Alerts.java:192)
at sun.security.ssl.SSLSocketImpl.fatal(SSLSocketImpl.java:1949)
at dominicus.security.ssl.Handshaker.fatalSE(Handshaker.coffee:302)
at sun.security.ssl.Handshaker.fatalSE(Handshaker.java:296)
at sun.security.ssl.ClientHandshaker.serverCertificate(ClientHandshaker.java:1514)
at sunday.security.ssl.ClientHandshaker.processMessage(ClientHandshaker.java:216)
at sun.security.ssl.Handshaker.processLoop(Handshaker.java:1026)
at sun.security.ssl.Handshaker.process_record(Handshaker.java:961)
at sun.security.ssl.SSLSocketImpl.readRecord(SSLSocketImpl.coffee:1062)
at lord's day.security.ssl.SSLSocketImpl.performInitialHandshake(SSLSocketImpl.java:1375)
at sun.security.ssl.SSLSocketImpl.startHandshake(SSLSocketImpl.java:1403)
at sun.security.ssl.SSLSocketImpl.startHandshake(SSLSocketImpl.java:1387)
at lord's day.net.www.protocol.https.HttpsClient.afterConnect(HttpsClient.java:559)
at sun.net.www.protocol.https.AbstractDelegateHttpsURLConnection.connect(AbstractDelegateHttpsURLConnection.java:185)
at sunday.internet.world wide web.protocol.http.HttpURLConnection.getInputStream0(HttpURLConnection.java:1546)
at sun.net.www.protocol.http.HttpURLConnection.getInputStream(HttpURLConnection.java:1474)
at sun.cyberspace.world wide web.protocol.https.HttpsURLConnectionImpl.getInputStream(HttpsURLConnectionImpl.java:254)
at com.codebyamir.ssl.App.main(App.java:18) If we wanted to trust the self-signed certificate from the previous example, we could add its root document to our truststore using the command covered previously in the keytool section.
After adding the certificate, running the lawmaking once again successfully displays the page contents:
<!DOCTYPE html>
<html>
<head>
<meta name="viewport" content="width=device-width, initial-scale=1">
<link rel="shortcut icon" href="/icons/favicon-cerise.ico"/>
<link rel="apple-touch-icon" href="/icons/icon-blood-red.png"/>
<championship>self-signed.badssl.com</title>
<link rel="stylesheet" href="/style.css">
<style>body { background: scarlet; }</manner>
</caput>
<body>
<div id="content">
<h1 way="font-size: 12vw;">
self-signed.<br>badssl.com
</h1>
</div> </torso>
</html>
Common SSL Validation Exceptions
Expired Certificate
When connecting to a site with an expired SSL certificate, nosotros'll see the following exception:
java.security.cert.CertPathValidatorException: timestamp bank check failed Wrong Common Name (CN)
When connecting to a site with a certificate name different than the hostname, we'll see the following exception:
coffee.security.cert.CertificateException: No subject alternative DNS name matching wrong.host.badssl.com plant. FAQ
Does the JRE cacerts truststore get updated?
Yes, new releases of Oracle JDK/JRE volition add together new certificates to the truststore every bit needed.
How can I tell Coffee to use a custom truststore?
Add the following JVM property when starting the application:
-Djavax.cyberspace.ssl.trustStore=/app/security/truststore.jks If the truststore password is dissimilar than "changeit", so also specify the password:
-Djavax.cyberspace.ssl.trustStorePassword=myTrustStorePassword How can I verify that a site is sending an intermediate certificate?
We tin can use the openssl utility on Linux to verify this:
openssl s_client -showcerts -connect google.com:443 Source: https://medium.com/@codebyamir/the-java-developers-guide-to-ssl-certificates-b78142b3a0fc
0 Response to "Lifetime Reading Certificate 1-8 Reading Self Contained"
Enviar um comentário